As cybersecurity gains importance, so does CISO influence in the buying circle
According to new findings from IANS Research, chief information security officers with executive-level titles now outnumber those with vice president or directory-type titles. It’s a trend that has been building for a few years, said the cybersecurity advisory firm, but this is the first time one of its surveys showed the majority of security leaders holding an executive-level title.
It’s also a trend that appears across business sizes, as IANS “State of the CISO 2026 Benchmark Report” found that 47 percent of large enterprises have raised security to the executive ranks, up from 33 percent in 2023. Among companies with annual revenue of less than $100 million, 52 percent of businesses now give their security leaders an executive or senior vice president CISO title.
“This year was a major turning-point year where it became a sufficiently large part of our sample that we were able to say are thought of as executive CISOs,” said Nick Kakolowski, senior director of CISO research at IANS.
And as the role of CISO evolves, it also expands. Just shy of 80 percent of CISOs surveyed recently for Cisco’s Splunk division said their role has become “significantly more complex.”
“They are now architects of trust and resilience for the entire organization, responsible for data privacy, regulatory compliance, third-party cyber risk and so much more,” argued the Splunk study.
“The cybersecurity function continues to rise in prominence, expand in scope and gain visibility. Consequently, CISOs are increasingly expected to serve not just as technical leaders, but as enterprise-wide strategists,” concurred IANS researchers.
As CISO responsibilities transform from hands-on technical experts into strategic leaders influencing business decision-making, it becomes incumbent on partners and providers of business technology to understand the growing influence of CISOs within the entire IT buying circle. Even when a seller may not be speaking directly to the CISO or specifically discussing cybersecurity, they often still must speak to a CISO’s concerns and objectives.
“The CISO role is undergoing a seismic shift – they are no longer just security leaders but are increasingly pivotal business strategists,” noted Kakolowski.
The IANS study categorized CISOs into three distinct segments based on their organizational influence and executive access. For this year, it found that 28 percent of CISOs were “strategic,” described as leaders who excel in both C-suite access and boardroom influence, frequently engaging with top executives to align cybersecurity with broader business goals. Half of CISOs were categorized as “functional,” meaning they have “significant influence” in either the C-suite or boardroom but lack consistent visibility in both areas. The smallest group, at 22 percent, was listed as “tactical.” These CISOs face limited access to senior leadership and infrequent engagement with the board.
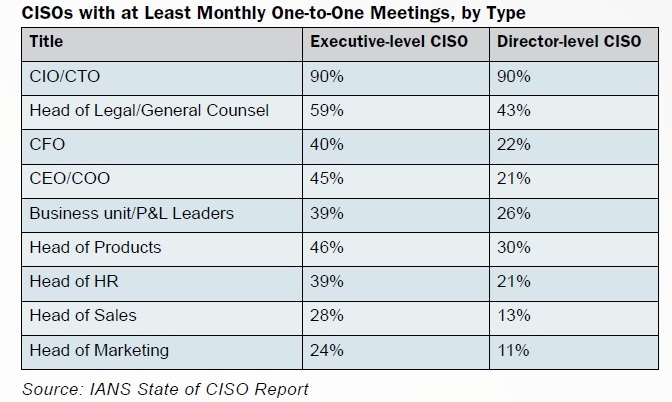
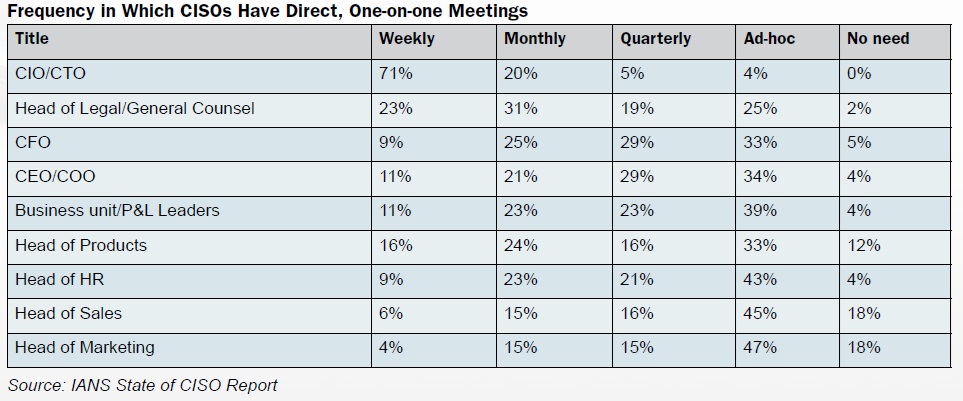
Not surprisingly, the senior executives that CISOs interact with most regularly are CIO and CTO types. According to the IANS survey, 91 percent of CISOs reported that they engage directly with their CIO or CTO at least monthly. The next most frequent interactions according to IANS figures were with general counsel or head of legal, which 54 percent of CISOs meet with at least monthly, followed by head of product, with which 40 percent of CISOs meet at that same frequency.
Elsewhere across the C-suite, just more than a third of CISOs reportedly meet with the CFO at least monthly, while 63 percent said they meet at least quarterly with the CFO. Very similar percentages said they meet with the CEO/COO at least monthly or quarterly, as well as with business unit/P&L leaders. And nearly half (47 percent) of CISOs engage with their boards on a monthly or quarterly basis, showed the IANS survey.
The prevalence of interactions between CISOs and both CFOs and legal officers also should not be surprising, as CISOs often get their funding from the CFO, while legal often directs cyber-incident response efforts, meaning these roles truly help CISOs get the job done, argued the Splunk report.
According to Splunk field CTO Peter Sprenger, CISOs working closely with the entire C-suite isn’t just about playing nice. It’s about joint accountability, and “it’s a business imperative,” said Sprenger.
When a CISO shares some responsibility for business deliverables, and all executives have skin in the cybersecurity game, organizations are better positioned to manage risk and adapt to regulations without sacrificing innovation or business success, Sprenger continued. Establishing shared planning cycles helps cyber defense to become proactive and embedded across the entire business.
Joint accountability, according to CISOs surveyed by Splunk, tops the lists of factors in terms of driving value for security initiatives (62 percent), ahead of even security budget and funding (55 percent) and access to security-relevant data (49 percent). At the same time, survey data showed that CISOs who share joint accountability for their security budget with non-technical C-suite
peers are more likely to say they can directly correlate ROI to risk mitigation and remediation activities (35 percent versus 25 percent). The same goes for those who work directly with their technical peers on security budgeting efforts (35 percent versus 20 percent).
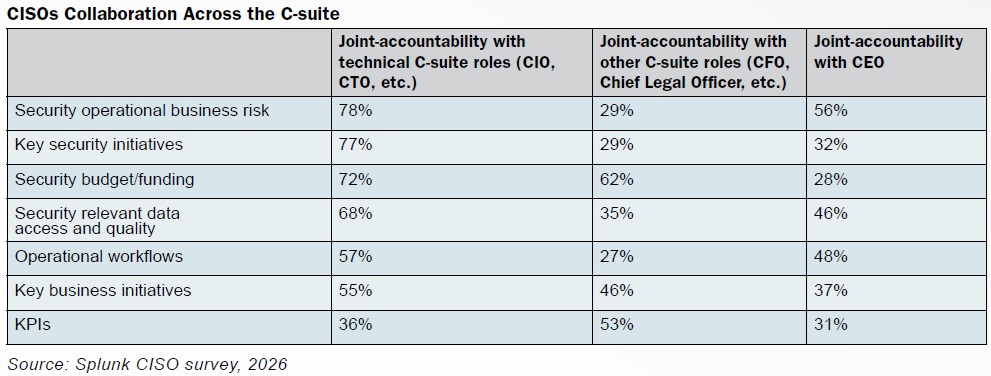
“Such collaboration is required for effectively integrating cybersecurity into business strategy, aligning risk management with organizational priorities and fostering a shared sense of accountability for security outcomes,” said the IANS reports.
Indeed, the increasing degree of cross-functional collaboration between CISOs and non-IT business leaders is a direct result of the expanding importance of cybersecurity within business processes and thereby the expanding role of security leaders within business operations. This is more profound nowhere than in the emergence of artificial intelligence. According to the Splunk surveys, a whopping 96 percent of CISOs said they are now responsible for AI governance and risk management, making them the de facto AI policy leaders at their organizations, said Splunk researchers. In many ways, it’s up to CISOs to make sense of the AI madness, strategically embracing AI while building robust guardrails around its use, ensuring that innovation serves security instead of compromising it.
“As boards mandate AI use across the business, CISOs must proactively manage risk to safeguard their organizations,” said Splunk researchers. “This means establishing a robust governance framework that enables safe AI, ensuring the pursuit of new capabilities doesn’t introduce critical vulnerabilities.”
Incidentally, but worth always keeping in mind, 78 percent of CISOs rank data leaks as their top concern with AI, according to Splunk’s figures. Second on the list was shadow AI, which presents a direct challenge to governance, control and the integrity of security operations. The third most common AI concern was the potential negative effects of hallucinations, such as misinformed decision making at scale.
Rolling Responsibilities
Beyond the realm of AI, the functional scope of the CISO role continues to expand into adjacent domains, suggests more than five years of IANS survey data, supported by ongoing conversations with CISOs. In this year’s survey, 53 percent of CISOs reported their responsibilities have grown during the past 12 months, a reality that holds true across organizational sizes and industries.
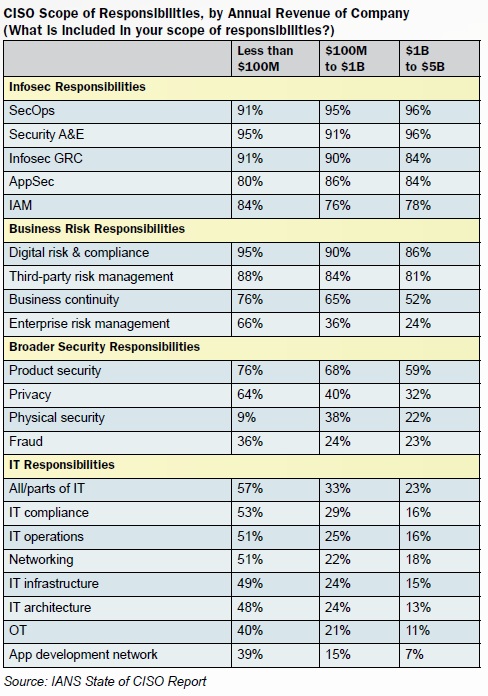
Information security remains at the core of CISOs’ responsibilities, with that vast majority overseeing elements such as SecOps, security engineering and architecture (A&E), government and risk compliance (GRC) and application security (AppSec) – and, increasingly, identity and access management (IAM). More recently, however, many CISOs have seen their portfolios broaden to include business risk functions such as third-party risk management and disaster recovery, broader security responsibilities such as physical security and fraud, and general IT responsibilities such as networking and IT infrastructure.
The scope of responsibilities is broadening the most among the smaller companies in the IANS survey. For example, CISO ownership of IT stack functions is relatively common at firms with $100 million in annual revenue or less but rare in billion-dollar enterprises. According to the IANS data, 57 percent of CISOs at firms with $100 million or less in revenue oversee all or part of the IT stack, including more than half who are responsible for networking, IT compliance, IT operations and infrastructure.
“These differences reflect the resource dynamics between small and large organizations: smaller firms often consolidate roles for efficiency, while larger companies allow CISOs to focus on core security strategy and leadership,” said IANS researchers.
Partners and providers looking to leverage CISOs’ newfound influence within buying circles can start by empathizing with the challenges and frustrations that come with their broadening roles. After all, a quarter of CISOs reported that their scope of responsibility is not consistently manageable, while an additional 28 percent said outright it is no longer tenable. Top concerns related to expanding scopes include teams that are too lean for organizational size and complexity, new mandates that are made without new resources, ambiguous reporting lines, inheriting broken systems and teams that must operate in constant triage mode.
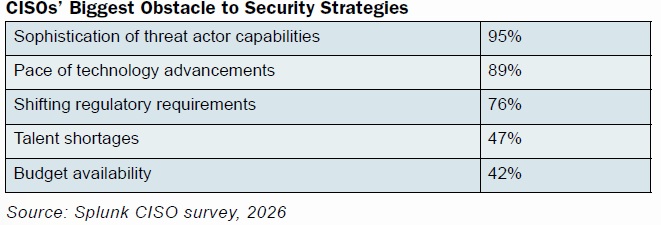
According to CISOs surveyed by Splunk, areas that need the most help within their security programs are threat hunting, engineering support (for vendor tooling, detection engineering or maintenance), software development, and network and cloud architecture. “These gaps
are especially painful to CISOs as they undermine the ability to address their top challenge, the growing sophistication of threat actor capabilities, and their top priority, improving threat detection and response,” said Splunk researchers.
While they navigate their rapidly expanding roles at the executive level, CISOs and their teams also are withstanding an onslaught of alerts. A full 98 percent site “high alert volume,” as a driver of stress, while 94 percent likewise list the high false alert volume.
“This isn’t just a nuisance; it’s a crisis of context, where critical insights and real threats get buried under a mountain of noise,” said Splunk researchers. “It’s difficult to prioritize alerts when everything feels urgent.”
About 80 percent of responding CISOs view tool sprawl as a source of stress, as well, calling into question solution providers who simply want to throw more products at security teams.
When asked to identify the greatest threats to executing their cybersecurity strategies, CISOs expressed a dual challenge. Externally, they confront increasingly sophisticated threat actor capabilities. “Gone are the days of obvious phishing emails filled with bad spelling and grammar. Today’s attacks are far more bespoke and convincing,” said Splunk researchers. Internally, they must orchestrate and manage budget, talent and executive buy-in to mount their defense.
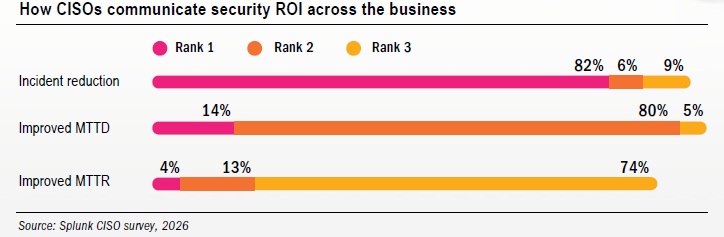
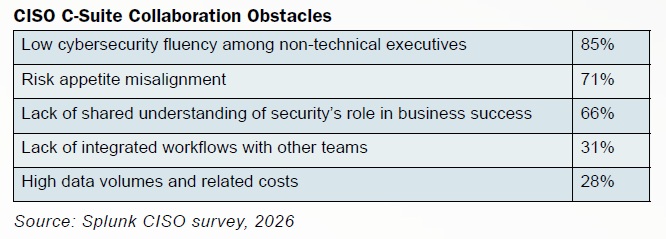
Executive-level CISO, in particular, must now more than ever translate the complex and often chaotic world of cybersecurity into clear-cut business value, Splunk’s data suggested. Low cybersecurity fluency among other C‑suite leaders is the most significant hurdle to cross-department collaboration, named by 85 percent of respondents. In other words, while CISOs recognize value in these partnerships, cyber knowledge gaps create tension.
“They’re asked to prove worth, justify investments and demonstrate progress to a board and C-suite that require clarity, but don’t always understand technical nuance,” said Splunk researchers.
Historically, cybersecurity has been seen as a cost center, but CISO are now beginning to frame it as a business enabler. According to Splunk CISO Michael Fanning, “CISOs shouldn’t expect leadership to inherently understand security’s value. We have to showcase it – proactively.”
Partners and providers that can help CISOs traverse this communications gap will no doubt be rewarded.











